GIS
Home » GIS
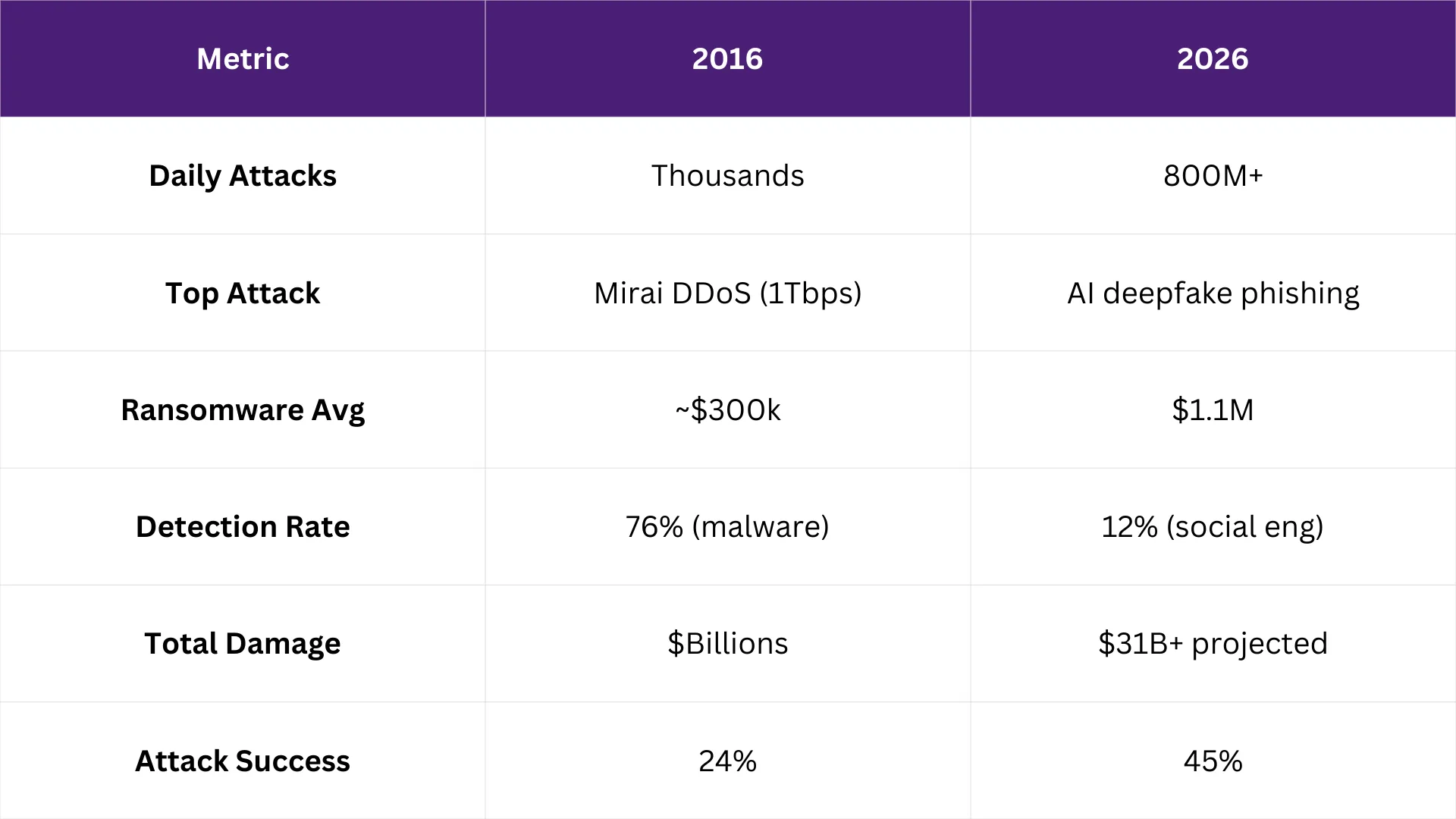
Traditional vs Modern Cyber Defence
March 31, 2026
A firewall and an antivirus subscription used to be enough. Not anymore. Cyber threats in 2026 have outpaced the tools ...
Hybrid Hive: March 2026 Newsletter
March 12, 2026
Managed IT support in Ireland means staying ahead of what’s coming, not reacting to what’s already happened. Deadlines, threats, and ...
House Analogy Series: Locked Down Internal Network as a Boundary Wall
February 24, 2026
Picture a property with a solid front door but no boundary wall. Once someone gets onto the site, they can ...
Hybrid Hive: February 2026 Newsletter
February 11, 2026
Data Privacy in Practice is more important than ever. January reminded us how fast cyber threats are growing and how ...
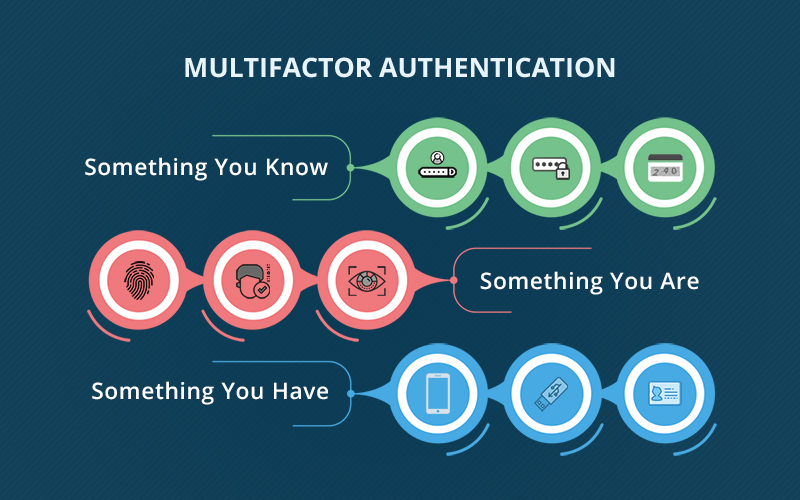
House analogy series: MFA is your double lock on the door
January 20, 2026
A stolen password is just a copied key. Multi-factor authentication adds a second lock that stops the most common way ...
Hybrid Hive: January 2026 Newsletter
January 13, 2026
Start 2026 with clarity and confidence A strong start to the year comes from knowing that technology is being taken ...
Hybrid Hive: December 2025 Newsletter
January 6, 2026
Looking back at 2025, we wanted to share the work that shaped the year and the impact it made for ...
House analogy series: Understanding Security Awareness Training (SAT)
December 4, 2025
In this latest episode of our House Analogy Series, we look at how managed Security Awareness Training (SAT) works like ...
Microsoft Windows Server 2016 End of life
December 4, 2025
Windows Server 2016 has been a trusted platform for many businesses. But its end of life is approaching, and that ...