Have you ever looked at your CCTV cameras the day after something happened?
You scroll through the footage and suddenly there it is — someone was inside. You missed it.
That’s exactly what it’s like when your business doesn’t have proper threat monitoring in place. You assume things are fine… but someone could already be in.
In this fifth part of our House Analogy Series, we’re talking about monitored SOC (Security Operations Centre). Specifically — Huntress, a 24/7 human-monitored cybersecurity solution.
What Is Huntress?
Huntress is a Security Operations Centre — real people watching over your systems, 24/7. Think of it like a monitored CCTV for your business, your computers, your emails and your devices.
It picks up what traditional tools miss. While antivirus might block basic threats, Huntress spots the threats your antivirus misses:
- Hidden malware buried deep in folders
- Suspicious logins from strange places
- Odd system behaviour and activity
- Hackers sitting quietly in your inbox
And when something is spotted?
A real human analyst steps in fast. Within minutes, they’ve reviewed it, confirmed the threat, and sent your team the exact steps to contain it.
It’s not just a warning or alert popping up on your screen.
Huntress tells your team what’s happening, how it happened, and what to do next.
Antivirus alone isn’t enough anymore.
But combine it with expert eyes on your systems 24/7?
You’ve got a proper safety net — the kind that stops real damage.
Why Does Monitoring Matter?
Most cyberattacks don’t come with flashing lights. Someone clicks a dodgy email. Nothing crashes. Everything looks fine. But behind the scenes, a hacker now has access. They don’t rush. They sit quietly. Watch. Wait for the perfect moment.
Without active monitoring, you won’t know they’re in until it’s too late. That’s how ransomware spreads. That’s how data gets stolen.
With Huntress, those silent threats get spotted early. It’s not just protection. It’s peace of mind.
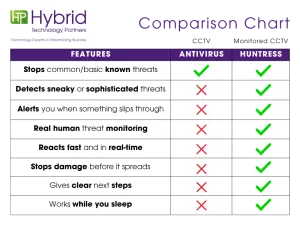
CCTV vs Monitored CCTV
Let’s break it down:
Real Example
A client of ours had an email account compromised after a staff member clicked a phishing link.
Five minutes later, Huntress picked up unusual sign-in activity and automatically raised a ticket. Our engineers acted immediately — they revoked the user’s sessions and MFA methods before the attacker could gain access again.
Because of that early warning, the situation was contained quickly. No data was accessed, and the business kept running as normal.
Think You’re Too Small to Be Targeted?
Hackers don’t go after businesses because they’re big.
They go after businesses that are easy to break into.
If you use email, cloud tools, or store customer info, you’re on the radar.
Most small businesses assume they’re too small to matter — they’re not.
Cyber-attacks often start with the ones who aren’t prepared. That’s why we keep watch, even when you think no one’s looking.
Free Download: 2025 Cyber Threat Report – Phishing Schemes
Want to see how phishing is evolving in 2025? Huntress has pulled together real examples and trends from the front lines.
Inside the report:
• Common phishing tactics attackers are using this year
• Real scam screenshots spotted by Huntress
• Tips to help you spot a threat early
Think You’re Covered? You Might Not Be.
Most breaches happen because businesses think they’re secure.
We’ll show you what’s in place, what’s missing, and how Huntress helps catch what antivirus can’t.
📩 Email mario@hybridtp.ie — before someone else finds the gaps.
Catch Up on the House Analogy Series:
• 🔐 Part 1: Door Access – Understanding Firewalls
• 🚗 Part 2: Vehicle Insurance – Datto 365 Backup
• 🛠️ Part 3: Breakdown Cover – Endpoint Backup
• 🚪 Part 4: The Front Door – EDR & Antivirus
• 📹 You’re here: Monitored CCTV – Huntress Monitored SOC
Written by: Jolene Oelofse – Marketing Lead, Hybrid Technology Partners
Jolene leads Hybrid TP’s content strategy, translating complex IT and cybersecurity topics into practical insights for Irish SMEs. She collaborates closely with the technical team and Managing Director Paul Browne to ensure every article reflects real-world accuracy and business value.